For a long time, password security was treated as a user discipline problem.
People chose weak passwords. They reused them across accounts. They clicked phishing links. The fix seemed straightforward: strengthen password policies, add MFA, and train users to behave more carefully.
That logic still explains part of the risk. It no longer explains the whole problem.
The issue now is less about whether users understand password hygiene and more about whether passwords still make sense as the center of enterprise identity security. In a threat environment shaped by infostealers, phishing kits, adversary-in-the-middle infrastructure, and large-scale credential abuse, the answer is increasingly no.
That shift is visible in the data. Verizon’s 2025 Data Breach Investigations Report found that compromised credentials were an initial access vector in 22% of breaches, while 88% of breaches in its Basic Web Application Attacks pattern involved stolen credentials. Microsoft’s 2025 Digital Defense Report says that 97% of the identity attacks it observed were password spray or brute-force attempts. Mandiant’s M-Trends 2025 report found that stolen credentials were the second most common initial infection vector in the incidents it investigated. IBM’s 2025 X-Force Threat Intelligence Index likewise pointed to a major increase in phishing-delivered infostealers.
Taken together, those findings suggest a different framing. Passwords are not failing simply because people misuse them. They are failing because the economics of identity attack have changed. What used to be a single control is now a reusable, tradeable, and highly scalable point of exposure.
Password weakness is no longer the main issue
It is still true that weak passwords create risk. It is also true that password reuse remains common. But those points can distract from the more important development.
Passwords are shared secrets. That is their weakness. Anything built around a reusable secret can be captured, replayed, relayed, or sold.
That mattered when attackers were working one account at a time. It matters more now that credential theft has become an ecosystem. Microsoft reports that 85% of usernames targeted in password spray attacks appeared in known credential leaks. Verizon, meanwhile, found a meaningful overlap between ransomware victims and the presence of their domains or employee emails in credential dumps. This is not just a story about careless users. It is a story about industrialized credential exposure.
That distinction matters because it changes what a “better password strategy” can accomplish. Stronger passwords can reduce guessing risk. They do much less against credentials stolen from browsers, harvested by malware, replayed from breach corpora, or relayed through modern phishing infrastructure.
So the problem is not merely that passwords are weak. It is that they are replayable. And replayable trust is increasingly hard to defend at enterprise scale.
Identity compromise now happens across a broader chain
Older authentication models were built around a fairly narrow assumption: if the login event is secure, the account is mostly secure.
That assumption is harder to defend now.
In many attacks, the password is only one artifact among several. An attacker may begin with phishing, not only to steal credentials directly, but to deploy malware designed to harvest browser data, cookies, session tokens, and saved logins. IBM reported a sharp increase in phishing campaigns delivering infostealers, while Mandiant’s incident data shows that stolen credentials continue to play a major role in initial compromise.
This is part of why passwords alone have become such an incomplete control. The modern attack path often does not depend on defeating the password in isolation. It depends on assembling enough identity material to earn trust.
A credential is exposed.
A session is established or hijacked.
A weaker recovery path is abused.
A second factor is relayed or socially engineered.
The attacker then moves from access to action.
That sequence is worth sitting with. It suggests that the real enterprise problem is not password theft as a standalone event. It is the broader ability of an attacker to obtain, preserve, and extend authenticated trust.
Once that becomes the frame, stronger password requirements begin to look more like a partial mitigation than a central strategy.
MFA remains necessary, but the category is too broad
This is where the conversation often gets compressed too quickly. Passwords are weak, so organizations deploy MFA. From there, the problem is assumed to be largely under control.
That conclusion is too neat.
MFA still matters enormously. Microsoft says modern MFA reduces the risk of identity compromise by more than 99%, which makes it one of the highest-leverage controls available. But the term itself covers very different security properties.
An SMS code, a push notification, a time-based one-time passcode, a hardware security key, and a passkey are not equivalent forms of assurance. They sit in the same category, but they do not fail in the same way.
That distinction has become more important as phishing kits and adversary-in-the-middle tooling have matured. Some MFA methods still interrupt basic credential stuffing. Others hold up better against real-time relay attacks. The point is not that MFA is insufficient. It is that enterprises need to think more carefully about which kinds of MFA meaningfully resist the attack patterns they now face.
That is also where standards guidance has moved. In the final NIST SP 800-63-4 Digital Identity Guidelines, phishing-resistant options are now required to be available at AAL2, while AAL3 requires phishing-resistant authenticators with stronger protections. Microsoft’s recent security guidance has moved in the same direction.
This is a subtle but important shift. The question is no longer whether an organization uses MFA. The question is whether it uses authentication factors that meaningfully resist phishing, replay, and relay.
Passkeys are gaining traction because they change the trust model
A useful way to think about passkeys is not as a consumer convenience feature, but as a change in authentication architecture.
Passwords depend on a shared secret. Passkeys do not. They rely on asymmetric cryptography, where the private key remains on the user’s device or authenticator and the service stores only a public key. That matters because it removes much of what makes passwords attractive to attackers in the first place.
The significance of that design is beginning to show up in both research and enterprise adoption. A 2024 USENIX Security paper on FIDO2 deployment found that organizations saw strong security and usability benefits in passkeys, even while confronting practical rollout challenges around recovery, compatibility, and operational design. The FIDO Alliance’s enterprise guidance makes a similar case: passkeys reduce dependence on replayable secrets while making strong authentication easier to deploy across more user journeys.
Large platforms are reinforcing the same direction. Microsoft’s update on advancing passkey adoption presents them as both safer and simpler than legacy sign-in methods. Amazon has likewise said that more than 175 million customers have enabled passkeys, with sign-ins occurring more quickly than with password-based flows.
None of that means enterprises can move overnight to a fully passwordless state. Most will not. Recovery design, cross-device portability, legacy systems, and internal adoption all complicate the path. But the direction is clear. Passkeys are being taken seriously because they address the underlying weakness of the password model, not just because they streamline the user experience.
The larger shift is from authentication as an event to authentication as a decision system
This is where many enterprise strategies still lag. Even when organizations adopt stronger factors, they often continue to think about authentication as a gate at the start of the session. Once the user is in, trust is assumed to persist unless something obviously breaks.
That is increasingly misaligned with how identity attacks work.
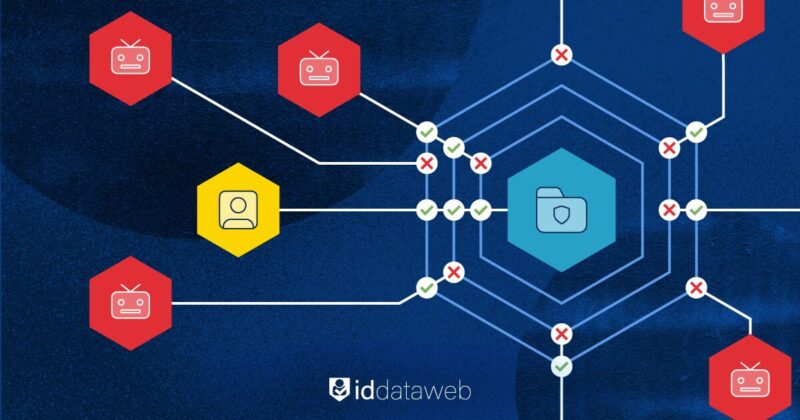
A valid credential is no longer strong evidence by itself. Nor is a successful MFA prompt. What matters more is the surrounding context: device integrity, network reputation, behavioral consistency, credential exposure, session continuity, recovery risk, and transaction intent.
Seen this way, the future of enterprise identity defense is not just phishing-resistant login. It is continuous identity evaluation.
That means authentication should not end once a person proves possession of a factor. It should continue as a series of risk judgments. Does this session fit the user’s known behavior? Is the device trustworthy? Is the network anomalous? Is there evidence that the credential has been exposed elsewhere? Is the requested action proportionate to the assurance gathered so far?
This is where the conversation begins to move beyond password policy and into identity threat detection. A correct password should not carry the same weight it once did. It may still be useful. It should no longer be decisive.
What enterprises should be doing now
The practical implication is not “remove every password immediately.” The practical implication is to reduce the amount of trust the enterprise places in passwords alone.
That starts by deploying phishing-resistant authentication in the places where the cost of compromise is highest. Administrative accounts, sensitive workforce applications, regulated customer journeys, privileged transactions, and account recovery flows should not depend on easily replayed secrets.
It also means treating adjacent identity processes as part of the same control surface. Password reset, help-desk verification, device registration, onboarding, session persistence, and recovery logic all need to be assessed with the same seriousness as primary login. In many cases, those paths are easier to abuse precisely because they were designed for convenience under older threat assumptions.
And just as important, enterprises need decisioning that extends beyond the moment of login. If valid credentials arrive from a suspicious device, from an anonymized network, or in a behavioral pattern that does not fit the account’s history, the correct response may be to step up assurance rather than accept the interaction at face value.
That is the deeper lesson here. The replacement for password-centric security is not a single new credential type. It is an architecture built around stronger authenticators, better recovery controls, and continuous risk evaluation.
Passwords are becoming one signal among many
This is probably the clearest way to state the change.
Passwords are not disappearing tomorrow. In many enterprise environments, they will remain part of the stack for years. But they are no longer reliable enough to serve as the organizing center of identity strategy.
Their role is changing. They are becoming one signal among many rather than the definitive proof of trust.
That is where enterprise programs need to move as well. Toward phishing-resistant authentication. Toward adaptive decisioning. Toward identity systems that assume credentials can be exposed without assuming that exposure must lead to compromise.
The organizations that do that well will not just have fewer password problems. They will have a more realistic model of identity risk. And that, increasingly, is what modern identity defense requires.