Most enterprise identity programs still treat login as the decisive moment. Once authentication processes mature beyond password dependency and enforce consistent multi-factor authentication (MFA), they are often considered “good enough” for digital trust. Phishing-as-a-service is changing the shape of the problem.
Phishing-as-a-service platforms help attackers obtain more valuable access, including valid sessions and vulnerable recovery paths into enterprise systems. Microsoft’s recent analysis of Tycoon2FA shows how mature this model has become. Microsoft describes the kit as one of the most widespread phishing-as-a-service platforms. It is tied to tens of millions of phishing messages that reach more than 500,000 organizations each month. Its adversary-in-the-middle capabilities allow less skilled actors to bypass MFA at scale.
Phishing-as-a-service has turned identity abuse into a supply chain. Attackers no longer need deep technical skills to run phishing infrastructure, proxy MFA, reuse stolen tokens, or pivot across channels. For defenders, keeping pace is difficult without visibility across the entire identity ecosystem. Security teams see successful authentication or a trusted account initiating a sensitive action. Help desks see a plausible user story during account recovery. None of those signals alone explain that an access decision is high risk.
The practical counter is not a single control. It is a technology stack that supports continuous identity threat detection and risk mitigation across login, session, recovery, and high-privilege actions.
Examining what phishing-as-a-service looks like
Europol’s Internet Organized Crime Threat Assessment describes an online criminal market where phishing-as-a-service is increasingly available. These services lower the level of organization and technical expertise required to commit fraud. The same report notes that phishing remains the most common attack vector in digital fraud schemes. Smishing is the most common phishing type, and QR-code phishing is rising in volume.
For enterprise security teams, these developments highlight two important trends. First, the market is making identity abuse easier to buy, operate, and scale. Second, the attack surface is fluid and spans multiple channels. When email becomes harder to exploit, identity fraud shifts to SMS. When users learn to distrust links, QR codes appear in PDFs and fake notices. When Web login flows become stronger, attackers shift toward help desks and recovery workflows.
The LabHost case illustrates the scale of these marketplaces. In 2024, the U.S. Department of Justice seized four Web domains used to create more than 40,000 spoofed websites. The phishing-as-a-service provider’s infrastructure stored more than one million user credentials and nearly 500,000 compromised credit cards. Calling LabHost a marketplace may understate its role. The phishing-as-a-service platform functioned more like an operating platform. It offered user support, scalable storage, and infrastructure that threat actors could use to build large operations.
How current enterprise defenses stack up
Most enterprises have not ignored identity security. Many have implemented single sign-on (SSO), MFA, and conditional access. Some are piloting passkeys. These are meaningful controls, but many still concentrate scrutiny at the front door.
This creates a blind spot when attackers use adversary-in-the-middle techniques to harvest the output of authentication rather than the authentication factor itself. The National Institute of Standards and Technology (NIST) has strengthened its guidance in this area. NIST Special Publication (SP) 800-63B states that verifiers shall offer at least one phishing-resistant authentication option at Authenticator Assurance Level 2 (AAL2), and federal agencies must require phishing-resistant authentication for workforce access.
The reasoning is straightforward. Traditional one-time-passwords (OTPs) and telecom-dependent second factors can still be relayed, intercepted, or socially engineered. Phishing-resistant methods bind authentication to the legitimate origin and increase the difficulty for fraudsters.
Even so, phishing-resistant MFA is not a silver bullet. In environments that harden login, attackers often move to recovery and enrollment processes. Help desks may be convinced to reset a factor. Attackers can target dormant accounts or exploit enrollment vulnerabilities to register new devices.
Zero Trust principles help, but only partially. In practice, implementation varies widely. NIST SP 800-207 states that Zero Trust assumes no implicit trust based on location or asset ownership. Authentication and authorization are discrete functions performed before access to an enterprise resource is established. The core idea is to avoid treating prior success as permanent proof. That is a useful principle, but operationalizing it remains a challenge.
Surveying the solution space for enterprises
This is where enterprises can incur significant costs. One strategy is to add point tools for every new tactic. Another is to tighten authentication so broadly that legitimate users bear the cost. Neither approach is ideal.
A more useful framework evaluates controls based on where phishing-as-a-service creates leverage for attackers.
The first control layer is phishing-resistant authentication. This remains foundational because it reduces the supply of replayable credentials and weakens commodity adversary-in-the-middle kits. It is particularly effective in workforce environments where enterprises often control devices, user populations, and enrollment.
The second layer is hardening recovery, enrollment, and second-factor changes. Mature attackers are not deterred by MFA alone and will attempt to bypass it. Password resets, MFA re-enrollment, and call center interventions should be treated as high-risk events rather than routine administrative flows.
The third layer is session- and token defense. This area remains underdeveloped in many organizations because responsibility is fragmented. Identity and access management (IAM) teams manage login. Application teams manage sessions. Security operation teams monitor alerts. Fraud teams investigate risky transactions. As a result, no one consistently monitors the patterns that matter most after authentication. Examples include token reuse from an unfamiliar context, mailbox rule creation after an unusual sign-in, or a benign-looking session followed by a payment change or a new payee.
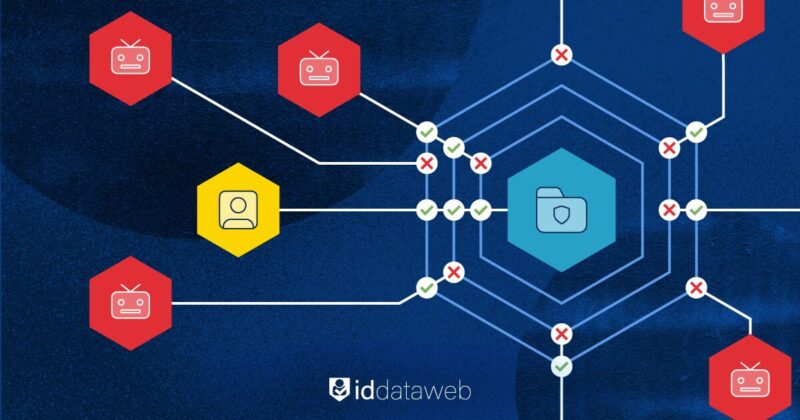
The fourth layer is continuous identity threat detection and risk mitigation. This layer connects the others. It correlates risk signals across identity, device, network, application, and transaction context. Based on those risk signals, it decides whether to allow, challenge, throttle, deny, or escalate access. This approach moves enterprise defenses beyond one-time trust decisions and toward contextual decisions based on evolving risk.
Contextual decision-making is important because every control introduces costs. Enterprise security strategists cannot rely solely on declining identity fraud metrics to judge success. They must also assess user friction and the operational burden created by controls. Excessive manual review can unintentionally increase identity fraud risk. Effective identity security balances detection with careful placement of friction.
Where identity threat detection and risk mitigation sits
Enterprises need a way to make consistent, contextual decisions across identity events without rebuilding every workflow from scratch. ID Dataweb operates in this space. It does not replace existing identity infrastructure. Instead, it acts as a threat detection and orchestration layer that coordinates risk signals and enforcement across channels and applications.
This matters because phishing-as-a-service has changed the core problem. Weak authentication is no longer the primary issue. Defender lag is. Identity fraud kits evolve quickly, and attack infrastructure is easier to purchase than enterprise defenses are to update.
Enterprises that rely on fragmented or heavily customized controls struggle to keep pace. In theory, a large organization can build identity threat detection internally by stitching together telemetry, risk rules, policy engines, case management systems, and integrations across IAM, identity fraud, and application teams. In practice, that approach is expensive and difficult to maintain. Phishing-as-a-service evolves too quickly for internally built systems to remain effective without constant investment.
Speed and efficiency matter because fraud-as-a-service is fundamentally a scale problem. Defenders need a model that can adapt at comparable speed. A SaaS-based orchestration and threat detection layer changes that dynamic. It reduces the time between recognizing a new attack pattern and deploying a response.
With a SaaS-based identity threat detection and risk mitigation platform, enterprises can adjust policies, introduce new risk signals, and strengthen high-risk workflows without long development or procurement cycles.
Conclusion
Fraud-as-a-service platforms allow fraudsters to compromise identity with greater ease and scale. As a result, traditional comfort signals such as successful MFA, normal-looking login telemetry, or a trusted phone number can no longer carry the same level of trust.
A mature defense strategy still begins with stronger authentication, especially phishing-resistant methods. However, it cannot end there. Enterprises also need continuous identity threat detection and risk mitigation across sessions, recovery paths, enrollment events, and sensitive actions. Risk must be evaluated continuously, not only at onboarding or login.
Identity threat detection therefore, becomes a critical component of enterprise cybersecurity strategy. It allows organizations to move from static trust decisions to continuous risk evaluation and from isolated controls to coordinated responses. In an environment where identity compromise is packaged, sold, and scaled like a service, enterprise defenses must become just as adaptive.