In The News

- Team ID Dataweb
The latest from ID Dataweb
- Press Release

- Team ID Dataweb
- Press Release

- Team ID Dataweb
- Press Release

- Team ID Dataweb
- Press Release

- Team ID Dataweb
CENTREVILLE, VA, January 20, 2026 – ID Dataweb today announced the appointment of industry veteran Dr. Torsten George as the company’s first Chief Marketing Officer (CMO). In this role, Dr. George will lead the company’s global marketing strategy, with a

- Team ID Dataweb
- Media Coverage

- Team ID Dataweb
Recent case studies
A leading eCommerce giant reduced chargebacks to just 0.2%, earned $4.6 million in additional revenue, and achieved a 99.5% approval rate by integrating ID Dataweb’s identity verification with their AI-driven risk assessment.
Learn how the Fast Tap MFA solution slashes user friction while delivering a powerful defense against phishing, SIM swaps, and account takeovers.
See how healthcare providers are accelerating patient onboarding, achieving a 95% verification rate, and cutting costs with the new Light Verification solution from ID Dataweb and Ping Identity.
Rewards program fraud is costing the hospitality industry over $1 billion a year. Learn how ID Dataweb is helping security-forward organizations meet the challenge.
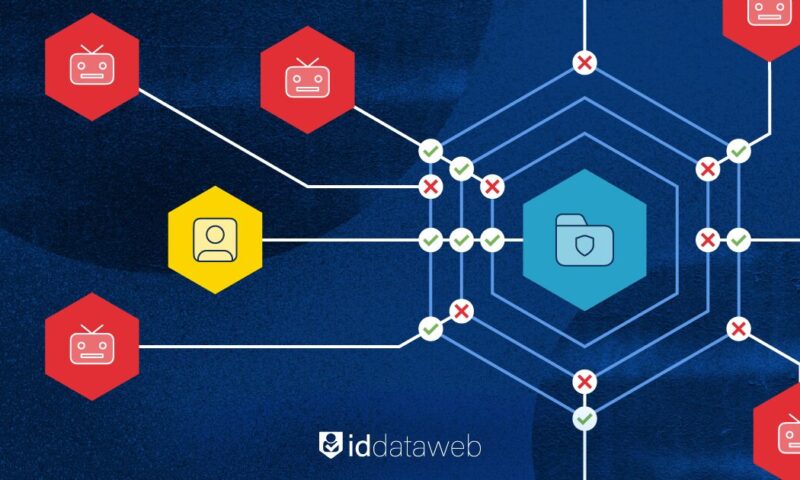
Eliminate account takeovers and synthetic identity fraud across every channel with ID Dataweb’s integrated verification engine.
Stop account takeover fraud using ID Dataweb’s integrated risk-based authentication and identity verification.