Synthetic identity fraud explained—and how a decision engine stops it
Multiple studies now attribute “over 80 percent of all new-account fraud” to synthetic personas. Enterprise security teams need the technical power to weigh thousands of risk signals in real time to stop synthetic identities from onboarding.
The Machine Identity Problem in Counterfraud Operations
In fraud prevention, robust machine identity is as critical as user identity – if you can’t trust what device is on the other end, you can’t fully trust the user.
How to secure yourself from credential stuffing account takeovers in 2025
Credential stuffing flourishes where reused passwords meet static login flows. Using ID Dataweb’s millions of risk signals, security teams close that gap without frustrating customers.
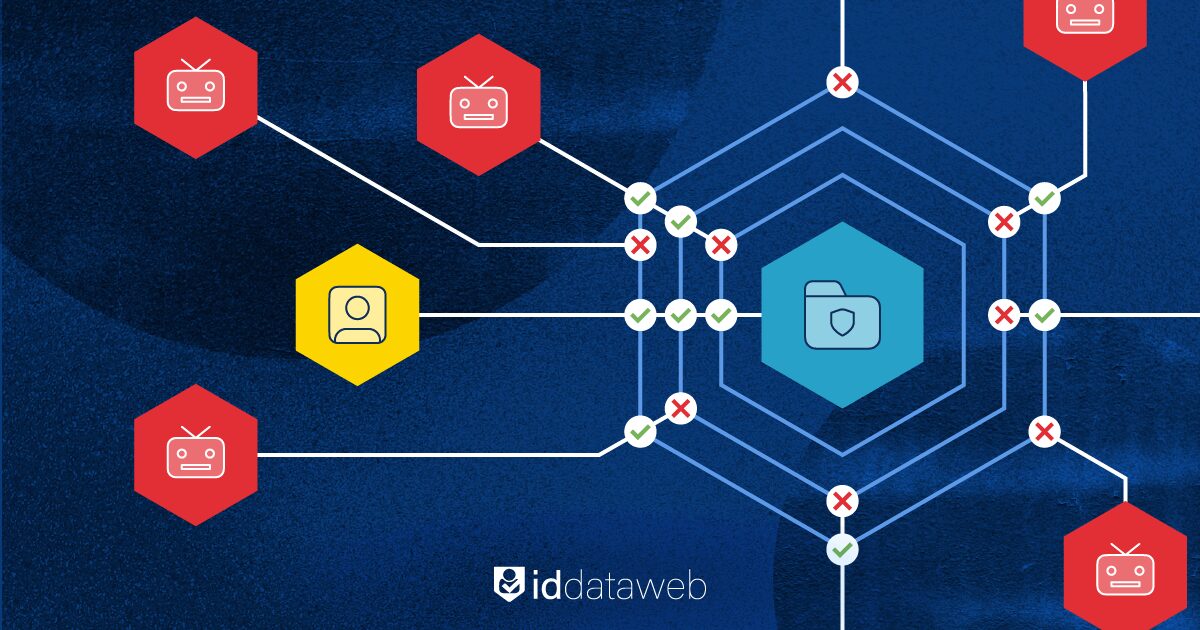
How policy & decision engines counter account takeover fraud
Businesses that rely on static fraud rules or isolated authentication checks risk account takeover attacks. Decision engines that leverage real-time risk signals allow organizations to battle new fraud tactics.







