How State and Local Government Agencies Can Shut Down Identity-Based Attacks
This blog examines how traditional identity verification and access management controls are increasing risk for state and local government agencies. It also explains how identity threat detection and risk mitigation can strengthen existing defenses and better protect public sector systems.
Why IAM Implementations Struggle and How to Get Them Right: 6 Enterprise Checklists
With compromised credentials now reported as the most common attack vector, Identity and Access Management (IAM) has become central to enterprise cybersecurity. This guide outlines 6 key considerations for an IAM program to succeed.
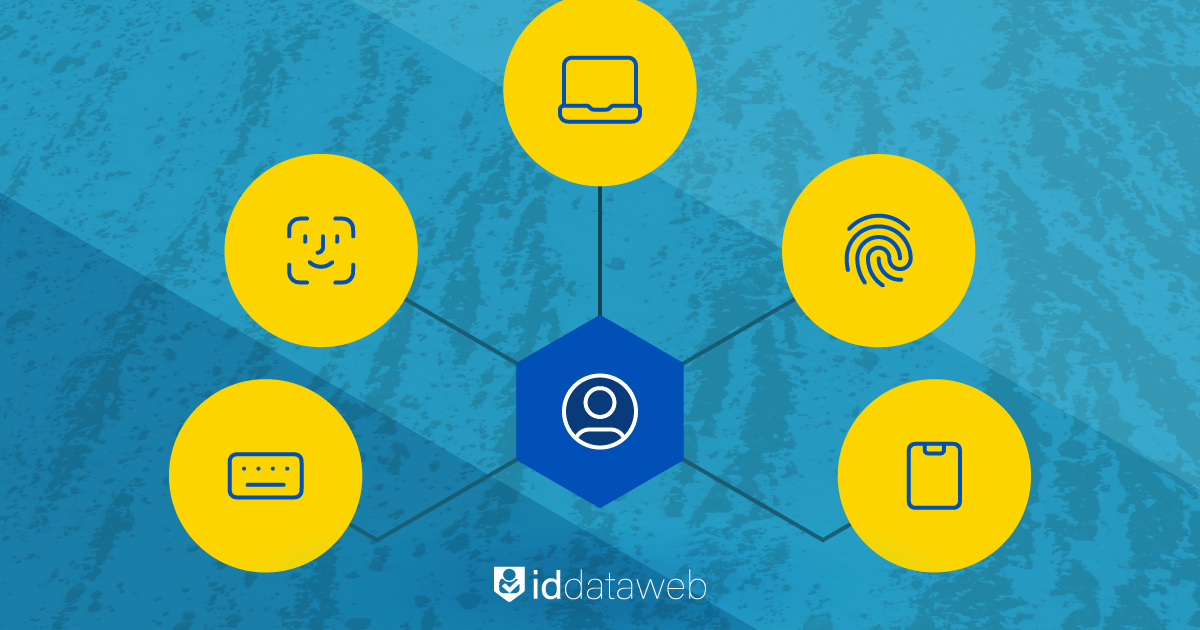
Decentralized identity and universal identity proofing

Decentralized identity models have emerged as a potential solution that balances user privacy with businesses’ digital identity proofing needs. While adoption remains limited, their ability to protect personal data while enabling universal identity proofing makes them an appealing path forward. The question is whether decentralized identity is truly the future of digital identity proofing, and if so, what has slowed its adoption.
ID Dataweb announces integration with Microsoft Entra ID
ID Dataweb has integrated its identity threat and risk mitigation capabilities with Microsoft Entra Verified ID, helping organizations proactively detect and mitigate identity risks before credentials are issued and maintain trust throughout the entire credential lifecycle.
Thwarting Modern Account Takeover Chains with Identity Threat Detection and Response
Modern enterprises, have invested in firewalls, encryption, and authentication. Yet call centers often remain a soft target. Agents have the authority to reset passwords and MFA. In modern account takeover (ATO) chains, identity—not credentials or firewalls—is the frontline.
Identity at the Core: How the Palo Alto-CyberArk Deal Changes Cybersecurity

Palo Alto Networks (PANW) announced its intent to acquire CyberArk, a leading Identity Security company. Identity Security has already been gaining momentum over the last year, and PANW’s acquisition further cements identity’s central role in modern cybersecurity.
Managing Joiner-Mover-Leaver Risk in 2025 with Automated Onboarding and Offboarding
Joiners need instant, precise access; movers collect too many privileges over time; leavers leave ghost accounts. Without automated provisioning and deprovisioning, and identity risk management, every stage elevates risk.
Automating Workforce Identity Management with an Orchestration Platform
If you’re an IT administrator, you know the pain of traditional workforce identity management. Provisioning accounts, verifying identities, handling contractors, disabling access for departures. Identity orchestration simplifies IAM.
The Critical Role of Identity Proofing for External Identities in Access Governance
Organizations today rely heavily on a mix of contractors, vendors, gig workers, franchisees, and partners. As a result, enterprises must rethink how to onboard external users swiftly, but with enough rigor protect sensitive systems and data.
5 IAM Trends to Watch in 2025
Five trends shaping IAM this year that enterprise security professionals and business leaders should watch closely.







